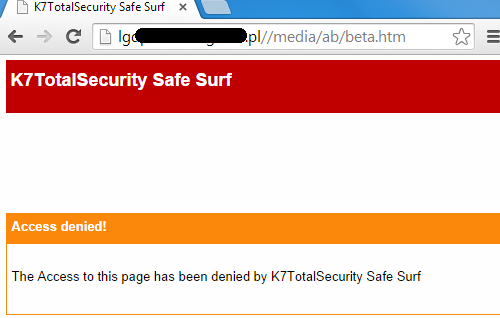
Are you excited about the new social networking platforms, games, mobile apps and the Internet of Things? Yes? Great, but BEWARE, hackers too are excited! With the K7 product installed, while visiting a website have you ever hit upon the message, “Access denied! The access to this page has been denied by K7Total Security Safe Search”? If you have, good, you’re safe.
We at K7TCL process a huge number of suspicious website URLs everyday and identify many malicious ones, some of which are hosted at compromised or hacked websites (websites which are owned by legitimate entities but have been forcibly taken over by hackers without the owners’ knowledge). To provide better protection to the user, URLs identified as malicious, including phishing, fraudulent and malware-payload links are blacklisted and the product denies access to them. We have stringent quality assurance processes to ensure that we don’t block access to clean websites.
As we blogged earlier, we occasionally receive URL false positive reports from our clients for the websites that are indeed compromised. So we thought it would be a good idea to educate the public with a blog series covering:
- How a website is typically hacked
- Factors to identify a hacked website
- Role of software vulnerabilities (defects in software that can be exploited by hackers) involved
- Consequences to the user in visiting a hacked website, along with a few mitigation guidelines for the webmaster
This is the first chapter of my blog series that briefly describes hacked websites and the reasons for a website to be blacklisted.
Usually hackers and their automated bots, which are malware designed to infect a user’s computer and connect back to a central command and control (C&C) server, break into targeted website hosting by exploiting a web application vulnerability on the target. Targeting a massive user base, hackers often prefer to hack renowned legitimate sites that own heavy network traffic to propagate the hosted malware and infect a large number of users, or fraudulently suck information from them, even before it is identified that the website is hacked, as in the case of the recent Ebay hack. Compromised websites are either injected with a malicious script that downloads another malware on to a user’s computer or ends up redirecting to another malicious site. Such a hacked website remains infected until the webmaster identifies, assesses, and remediates threats to his/her systems.
In response to the aforesaid incidents, we duly inform the concerned authority, i.e. the webmasters, of such infected websites about the scenario and the recommended course of action. Therefore we recommend that webmasters provide accurate, up-to-date contact details on their domain registrations and DNS records so that we know whom to contact when the need arises.
To an end user visiting a compromised website with a vulnerable browser or browser plug-in may leave the user’s computer infected with a malware without his/her knowledge. So, it is advisable that users regularly apply update patches for their operating system and the other software they use.
A blacklisted website/URL satisfies one or more of the following criteria:
1) It redirects to a malicious link or points to a malicious payload
2) It is used in spam or phishing campaigns
3) It is hosted on a compromised web server
4) It contains malicious JavaScript code
Alexa, a well-known provider of web traffic information, ranks 1 million domains and sub-domains on a daily basis according to their popularity. To get an idea of the number of compromised and popular websites used in malicious attacks, we looked at how many malicious URLs are hosted on websites listed on Alexa’s top 1 million. From our latest lab data and instrumentation, we observe that currently approximately 7500 popular domains are compromised and 10791 exploit-related URLs are blocked by our product’s site blocker. Furthermore, out of these,16 sub-domains and 16 blocked URLs have domains ranked within Alexa’s top 100.
In the next chapter of my blog series, I will describe how websites get hacked in the first place, focussing on the vulnerabilities and exploits involved.
Priyal Viroja, Vulnerability Researcher, K7TCL
If you wish to subscribe to our blog, please add the URL provided below to your blog reader:
https://labs.k7computing.com/feed/








