The infamous ransomware malware works by restricting access to the computer or files that it infects. The malware on behalf of the malware author then demands a ransom to be paid by the victim, in order for the restriction to be removed.
At K7’s Threat Control Lab, we recently noticed a new wave of this ransomware malware. This notorious variant called CryptoLocker, by most security vendors, installs itself into the victims “Documents and Settings” folder. The malware then adds itself to the Windows auto start location in the registry to ensure that it loads automatically every time the user logs on.
Cryptolocker then makes an HTTP POST request to a pre-determined set of domain names to download a unique password file, using which it then encrypts the victim’s documents. The documents targetted include images, spreadsheets, presentations, text files among others.
Once encrypted, the ransomware then pops up a ransom page like the one displayed below:
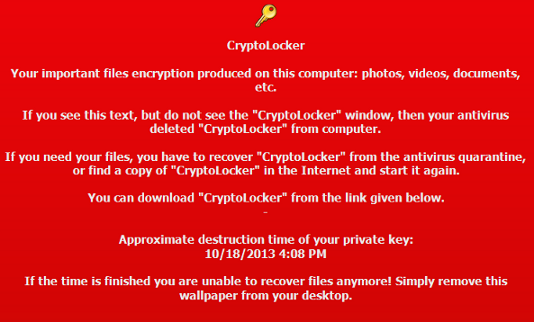
The malware gives the victim a limited amount of time, to buy the password file to unlock the user’s data.
Protection for this threat is provided at multiple layers by K7’s Threat Control Lab. We proactively detect both the spam emails and malicious URLs, used to spread this ransomware, which seem to be the current infection vector. In case the malicious content does get through this layer of protection, we detect the malicious files themselves by our on-access-scanner as Trojan ( 0000c3521 ) and Trojan ( 0040f66a1 ). We have also provided detection for the this ransomware based on its run time malicious behaviour.
Our usual sentiments about keeping one’s security solutions & Windows patches up-to-date and being vary of downloading files from unknown sites apply.
Lokesh Kumar
Malware Collections Manager, K7 TCL
If you wish to subscribe to our blog, please add the URL provided below to your blog reader:
https://labs.k7computing.com/feed






