Ransomware has always been a matter of concern for the cybersecurity landscape. A new entry has been seen recently which comes with the name as GIBCRYPTO. We will delve into the GibCrypto Ransomware’s destructive and evasion capabilities in detail.
According to VirusTotal the ransomware was first seen in Germany on Feb 22,2026 and has been spotted in other countries since then as shown in Fig 1.

Technical analysis
It is a .NET PE file. The time date stamp of the file has been 0’ed out.

The ransomware on execution locks out the victims system and shows the ransom note as shown in Fig 3.
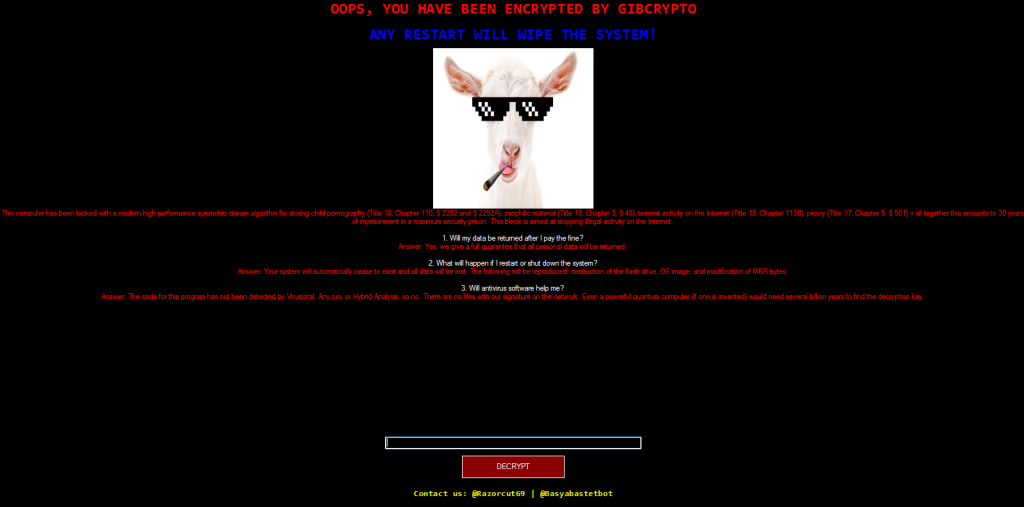
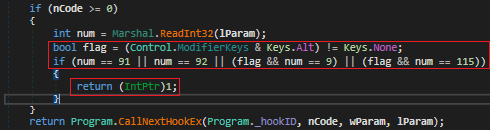
After the screen is locked with the note, the ransomware captures the keystrokes and blocks Alt key along with F4, Left windows key, Right windows key and Tab key. This combination of keys restricts the user from opening task manager or attempting to exit the lock screen. Capturing keystrokes is a feature we see in keyloggers. This ransomware is suspected to be a part of Snake Keylogger’s campaign which will be discussed later in the blog.
Now we will discuss some of its persistence and defense evasion capabilities.
It creates a run entry as shown in Fig 5.

It disables the real time monitoring of Windows Defender using Powershell cmdlet and disables the Windows task manager for current users.

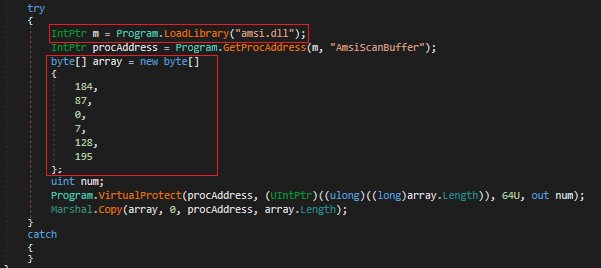
AMSIScanBuffer is a core function used by WIndows to scan Powershell script, VBScript, JScript,etc
Like many ransomwares it patches AMSI buffers so that Windows security services do not scan that memory region. The values in the array 187, 87, 0, 7, 128, 195 corresponds to the binary
B8 57 00 07 80 mov eax, 0x80070057 (57 decimal value = 87 E_INVALIDARG)
C3 ret
This code immediately overwrites the first 6 bytes of in-memory code of AMSIScanBuffer. EAX register holds the return value which is overwritten with 0x0057. Windows error code 87 being invalid parameter, forces the function to exit, skipping the scan altogether. This method is also called inline patching.
It deletes shadow copies using cmd.exe. This foils any attempt made by the victim to restore the system.

It also corrupts the MBR so that any restart of the system will cause the system to run into an error.
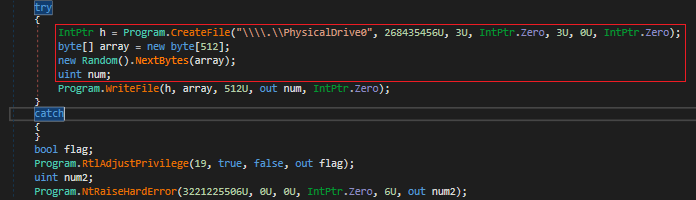
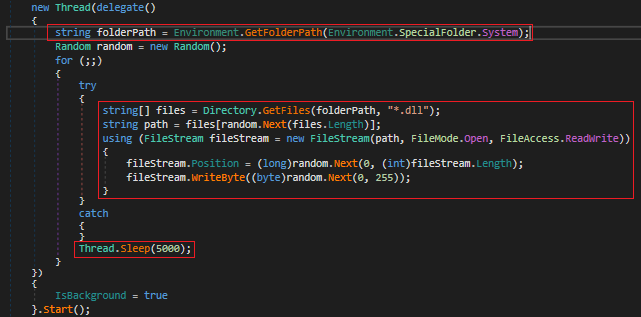
Not only does it corrupt the MBR but also it corrupts some of the essential Windows system dependencies. It randomly chooses system DLL files and tries to overwrite it with random bytes causing the system to run into BSODs, break services or cause random crashes. It keeps iterating through the DLLs and waits for 5 seconds after each corruption.
So this was all about its evasion and destructive capabilities. Now we will briefly discuss its encryption algorithm and an added espionage feature.
The ransomware encrypts the files and adds .gibcrypto extension to the encrypted files. It recursively iterates through all directories and their sub-directories, checks for the extension gibcrypto or any directory name containing the word windows as shown in Fig 11 to prevent duplicate encryptions or encrypting Windows files.

The ransomware uses the Salsa20 algorithm for encryption as shown in Fig 12. This function loads an entire file in RAM, array2 variable which generates a random 8-byte value for each file, encrypts the data in that file using Salsa20 algorithm, writes the new encrypted file in the same directory and deletes the original file. The randomly generated 8 byte value is also stored as an encrypted file in the same location.


The ransomware comes with an extra feature that lets the attacker get feedback whether the victim is compromised or not.

As seen in Fig 14, the ransomware creates an encrypted file with the victim’s username and machine name as file name and sends it over telegram using a bot token and chatID. It also captures the screenshot of the screen and sends it over the same chatID.
The bot token and the chatID are as follows :
Bot token: 8514918049:AAEyTqSuSZaPOdNZN08tL395l0SgCFg-ju8
ChatID: 7592909148
The investigation revealed that the bot token and ChatID used by the sample correspond to the same command-and-control (C2) infrastructure previously used by Snake Keylogger. Additionally, several technical characteristics—such as compilation using MSIL, the presence of keylogging functionality, espionage capabilities, screenshot collection feature and the shared C2 channel—align with the behavior and patterns observed in Snake Keylogger. It can be assumed that the same threat actors operating Snake Keylogger are also behind the distribution of the Gibcrypto ransomware.
Gibcrypto ransomware is one of the latest ransomware with highly destructive capabilities. After the overall analysis of the malware, it can be concluded that it is unlikely to get the files back even if the ransom is paid.
K7 Antivirus defends against these threats. Therefore, it is recommended to use a reputable security product like K7 Antivirus software and stay protected from such threats.
IOCs
| Name | Hash | Detection Name |
| Gibcrypto.exe | 1B56666BC5DB3351FC112245251620B2 | Generic Ransomware(Type1) |
MITRE ATT&CK ID REFERENCE
| Tactic | MITRE ATT&CK ID | Technique Name | Description |
| Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | Creates a run entry to ensure execution after system reboot. |
| Defense Evasion | T1562 | Impair Defenses | General category for disabling security features. |
| T1562.001 | Impair Defenses: Disable or Modify Tools | Blocks Alt, F4, Left windows, Right windows, and Tab keys, and disables Windows Task Manager. Disables real-time monitoring of Windows Defender using Powershell and patches AMSI buffers (inline patching) to skip security scans. | |
| T1490 | Inhibit System Recovery | Deletes shadow copies using cmd.exe. | |
| Collection | T1056.001 | Input Capture: Keylogging | Captures keystrokes while the victim’s system is locked. |
| Collection | T1082 | System Information Discovery | Collects the victim’s username and machine name. |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols | Sends an encrypted file containing victim info and a screenshot over Telegram using a bot token and chat ID. |
| Impact | T1486 | Data Encrypted for Impact | Encrypts files using the Salsa20 algorithm and adds the *.gibcrypto extension. |
| T1485 | Data Destruction | Corrupts the MBR and randomly overwrites essential Windows system DLL files with random bytes. |






