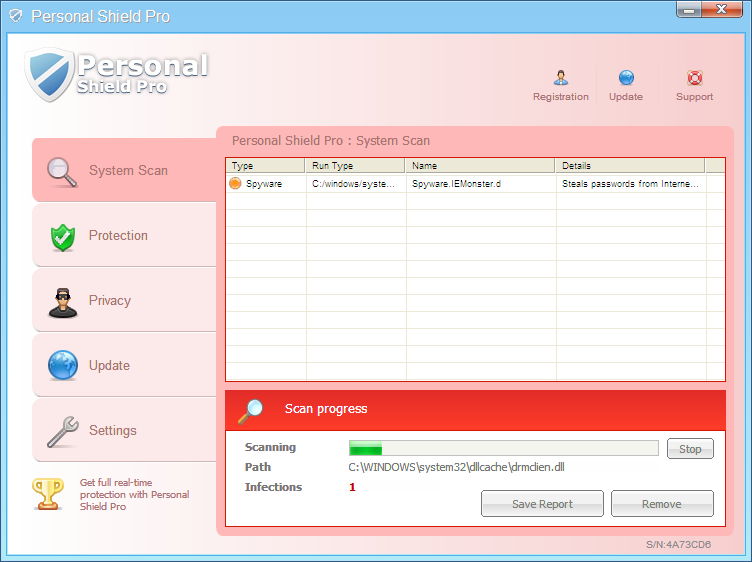
Over the past week we came across several client submissions of ‘Personal Security Pro’, one of those highly ambitious FakeAV families that are currently prevalent.
This FakeAV, upon installation and execution, terminates almost every executable running in your system, which includes even security products. The FakeAV copies itself to a randomly named folder as “%AppData%\<randomnamefolder>\<randomnamefile>.exe” and drops a RunOnce registry trace that has a value that is equally random as the filename and folder name.
This FakeAV has an unusual behavior insofar as it drops a RunOnce entry rather than the standard Run flavour. A registry RunOnce entry is a method provided by Windows to initiate any executable for one time only upon system reboot, the RunOnce entry being deleted thereafter. Hence the life of this registry entry is just one reboot. Thus when you boot back the system and search for any malicious traces in the registry you wouldn’t find any, however the FakeAV would have got initiated. This FakeAV, on getting executed, terminates most processes that are not core system processes. One of the executables it allows us to run is ‘Explorer.exe’. After terminating the processes it drops the RunOnce registry entry again. The cycle is repeated on the next reboot.
The functionality to terminate running processes and prevent new ones from starting up is done in an attempt to circumvent the clutches of security software. In fact, the RunOnce key is added in a strategically temporal manner to avoid it being flagged by HIPS (Host Intrusion Prevention System) rules, ubiquitous in Anti-Virus products these days. HIPS is a method of blocking dynamic malware activity. In the case of the K7 TS11 product, with its robust self-protection, the FakeAV’s attempts at termination are futile, and the malware file gets flagged and quarantined without a problem.
Kaarthik R.M
K7TCL








