Data privacy has always been one of the challenges pertaining to cyber security, and has therefore been one of the main focus areas for all, be it for an individual, organization or at the national level. Nobody wants their privacy meddled with. There has been a recent news about the on-going investigation by the Government of India in which Indian Intelligence agencies have listed 53 apps with links to China that impact data privacy. They claim that these apps exfiltrate Indian user information outside India and have advised users of these apps to uninstall them.
Listed below are some of the most popular apps that have been recommended for uninstallation:
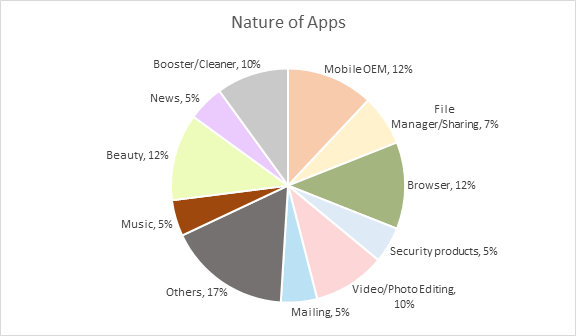
These apps are either directly or indirectly linked to a Chinese development environment and are categorised into various groups like Manufacturer apps, News, Browser, Security products, etc., as shown in the Figure.
The published list of apps may not be exhaustive as there could be other data privacy compromising apps from mobile manufacturers which are pending thorough investigation.
(Un)Ease of Uninstallation
Although many of the apps listed seem to fall into the category of general purpose apps like cleaner apps, browsers, chat messengers, video/photo editors, there are also apps like Mi Store and security products that might require “device administrator” or “system” privileges for uninstall. In fact, the uninstall process could vary depending on whether an app version from the device manufacturer or OEM is downloaded from the official Google Play/third-party store or whether the same app comes pre-installed on the device.
Therefore, from an end user’s perspective, the level of difficulty in removing these apps from an Android device varies based on the privilege with which an app was installed. An app’s privilege level can be one of the following:
- User : Regular user privileges – easy uninstall
- Device Administrator : Higher privilege than a user app – uninstallation same as a user app but requires deactivation of device administrator privileges
- System or Preinstalled (apps that come preinstalled on a brand new device) :
- Escalated privileges
- Apps installed in the system/kernel areas of the device
- Has the ability to collect any user or device information
- Is nearly impossible to be uninstalled by an end user unless the device is rooted, which is not typically recommended, as we discussed in one of our earlier blogs, “Preinstalled: Clean or malware system app?”
- Many OEM versions have been identified as unwanted applications or bloatware that not only exhausts the storage space but have also been observed to forward collected user information to the device manufacturers
Hence, uninstalling all of the listed apps will not be an easy task for the user.
Privacy Policy of an Application
In order to overcome and mitigate such users’ data privacy issues, Google’s policy for “Privacy, Security and Deception” of an app states how a developer is expected to explicitly inform the user in an app’s privacy policy (both in-app and in website) about:
- Why the user data is collected and the reason behind this
- How an app accesses, collects, uses, and shares user data
- Types of parties with whom any personal or sensitive user data would be shared
Although an app developer typically conforms to the above norms, generally, almost all of the users ignore reading the privacy policy for the most common reason that it is lengthy to read and deemed too time consuming, without realising the significance of it. Google insists on the privacy policy being read by the user so that they understand:
- List of Personally Identifiable Information (PII) like email address, phone number, device information, etc., collected by the app
- Why is that information collected?
- How is the data used and/or shared?
- Is the collected information really required for an app’s functionality? (For example, why would a “beautifier” app need to collect your geolocation information?)
Declaring the list of data collected from an app upfront and in simple terms aids visibility and readability rather than having to wade through privacy policy legalese. Thus, a user can make a conscious decision whether to install the app or not, unless it is preinstalled, of course.
The most important concerns are usually overlooked such as:
- Where are these collected data stored?
- Are they stored within a user’s national boundaries or on some remote server, perhaps even in hostile territory?
- How secure is the collected data?
- How frequently is data privacy monitored?
- Are users’ data used for any other purposes apart from the stated intended use?
A user’s sensitive and personal data could be endangered when they are stored on a remote server outside their homeland as legal constraints around PII policy might differ across borders, and they would have less control over the data stored. High profile users’ data could be more at risk, leading to cyber espionage among other cyber attacks.
Clearly the emphasis is on the usage of locally-produced mobile devices with data hosted on local servers bound by local laws to avoid any unwanted data exfiltration.
In addition, as always, users need to be vigilant about:
- Installing only required apps
- The extent and type of information which he/she is willing to share