A few months ago we highlighted the complications that could arise when different families of malware interact with each other. These scenarios take place on a regular basis, and for the most part involve file infectors, i.e. the quintessential “virus” type, which latch their code on to host executable files. Multiple infections of a given host, especially by different families of viruses, seriously complicate the process of disinfection to restore a suitable version of the original file. Let us take a brief look at the technical reasons for these complications.
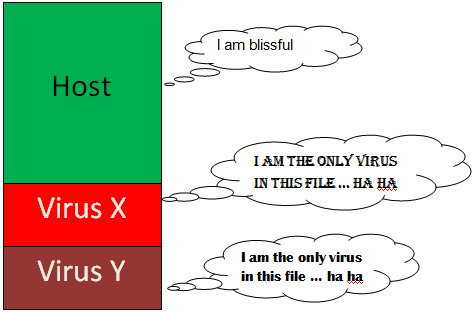
There are two main issues. The first is that viruses can interfere with each other to the extent that the original host file is permanently damaged, i.e. “corrupted”. This happens because most virus authors do not expect to infect a host which has already been infected with another file infector, and therefore do not design their code to deal with these scenarios. Consequently certain assumptions about the suitable physical characteristics of a host file to be infected may not hold true (hosts infected by a virus generally look very different when compared to typical clean files), and a subsequent infection simply breaks the erstwhile executable file. Of course, it is not straightforward to determine that a host file already contains a virus infection, especially if the infection involves function patching (aka mid-infection) rather than the far more common entrypoint change. One must also avoid confusing a host which appears odd due to its legitimate packer rather than due to a virus infection.
The second issue is somewhat related to the first, but from the perspective of making disinfection far more difficult, even when it is possible. The reason for this is that a disinfection routine, a very delicate process, almost always has to be exactly tailored to the specific virus at hand, with concomitant assumptions about the physical changes which require remediation. It is virtually impossible to reliably predict the presence of another virus infection, much less the specific virus family involved. Under these circumstances of multiple cross-family infections, any assumptions made in the disinfection routine for a known virus layer could be null and void, resulting in the attempted disinfection failing, or far worse, corrupting the file on which the operation is being performed.
The high prevalence of multiply-infected host files in India indicates the ubiquitous nature of several virus families vying for supremacy. There may also be the suggestion that users are not rigorous enough about keeping their Anti-Virus solution completely up-to-date since some of the virus infections seen involve “ancient” families which have been protected against for several years. Our usual sentiments about keeping one’s security solution up-to-date apply.
Samir Mody
Senior Manager, K7TCL







